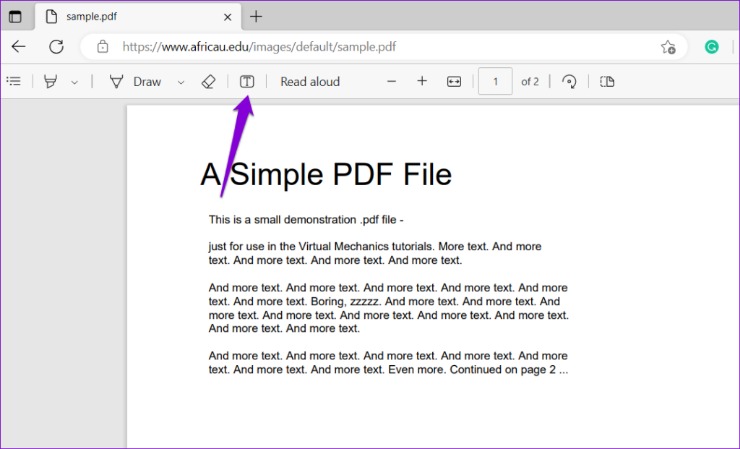
Upload: Drag and drop your PDF or image, or select it manually from your device via the dashboard. You can also connect to our API or document processing pipeline through Dropbox, Google Drive, Amazon S3, or Microsoft OneDrive.
Verify in Seconds: Our system instantly analyzes the document using advanced AI to detect fraud. It examines metadata, text structure, embedded signatures, and potential manipulation.
Get Results: Receive a detailed report on the document's authenticity—directly in the dashboard or via webhook. See exactly what was checked and why, with full transparency.
How modern tools and AI can quickly detect fake PDFs
Detecting a fake PDF today is no longer limited to visual inspection; modern systems combine multiple layers of automated checks to expose manipulation. At the foundation is a forensic scan of file-level properties: examining the metadata (author, creation and modification timestamps, application versions, and embedded fonts), cross-referencing timestamps with expected workflows, and identifying inconsistencies that suggest post-creation edits. AI and pattern-recognition engines then analyze the document internals—object trees, content streams, and embedded images—to find anomalies that humans often miss.
Optical Character Recognition (OCR) is a key component. When a PDF contains scanned content, OCR extracts the text layer and compares it to visible glyph patterns. Mismatches can indicate that text was overwritten or that images were resequenced. Text structure algorithms evaluate font usage, spacing, and ligatures; sudden changes in font metrics or character encodings inside a document are strong indicators of tampering. Additionally, embedded resources such as fonts, images, and JavaScript are scanned for suspicious payloads or unusual compression artifacts.
Cryptographic checks include validating embedded digital signatures and verifying checksums of attachments. A valid digital signature ties a document to a signer and a certificate chain; when signatures fail validation or are absent where expected, the document’s trustworthiness drops. For advanced workflows, automated systems correlate metadata with external sources (e.g., email timestamps, cloud storage logs) to detect improbable sequences of events. Together, these automated layers provide a reliable, fast path to identify suspicious PDFs and flag them for deeper human review or automated rejection.
Practical checks and technical signs to look for when analyzing PDFs
When you need to manually triage a suspicious document or interpret an automated report, prioritize a set of practical checks that reveal the most common forgeries. Begin with a careful inspection of file properties: open the PDF’s document info and review creation and modification dates, the producing application, and embedded user names. Discrepancies—such as a document claimed to be years old but produced by a recent software version—are red flags. Tools that parse the PDF structure can reveal hidden layers, appended pages, or removed objects that standard viewers hide.
Next, inspect text integrity. Use search functions and OCR to confirm that the visible words match the underlying text layer. If searching fails for specific passages, the text may be an image or an overlay. Look for visual artifacts around signatures, stamps, or logos: uneven pixelation, repeated patterns, or mismatched compression levels often indicate copy-paste edits. Check font embedding: missing or substituted fonts can alter character spacing and introduce subtle changes that betray manual editing.
Investigate embedded links and scripts. Malicious or forged PDFs sometimes contain hidden links or JavaScript that alter behavior on open; examine these objects for unexpected URLs or obfuscated code. Verify digital signatures by examining certificate chains and revocation status with trusted authorities. Finally, compare the PDF content against known templates or canonical copies using hashing or similarity analysis. A simple file hash mismatch indicates any modification, while similarity metrics help detect partial copying or template reuse. These pragmatic checks, combined with automated verification, make it possible to catch most forms of PDF fraud before they cause harm.
Real-world examples and case studies illustrating PDF fraud detection
Real-world incidents show how PDF manipulation can be subtle and sophisticated. In one corporate procurement case, an invoice appeared legitimate but was altered to divert payment to a fraudulent account. Forensic analysis revealed that the payment details had different layer properties and a mismatched font embedding compared to the rest of the document. Metadata timestamps showed that the document was edited after the original issue date, and a checksum comparison against the vendor’s archive exposed the tampering. This combination of metadata analysis and file hashing led to rapid recovery of funds and legal action against the perpetrator.
Another case from academia involved falsified transcripts. At first glance, the PDFs matched institutional templates perfectly, including seals and signatures. However, AI-driven analysis detected subtle inconsistencies in the seal’s raster pattern and an unexpected color profile for the stamp image. Cross-referencing the embedded certificate in the apparent signature with the issuing authority’s records showed it was self-signed and not part of the institution’s certificate chain. The institution updated its validation procedures and began requiring cryptographic signature verification for all official documents.
Legitimate services designed to detect fake pdf offer integrated workflows that replicate these forensic steps at scale. They provide automated ingestion (via upload, cloud connectors, or API), instant AI-driven validation, and transparent reports detailing which checks passed or failed. Organizations using such systems have reduced payment fraud, prevented forged credential acceptance, and streamlined compliance audits. These examples underline that layered detection—combining human judgement with automated checks like metadata verification, OCR consistency, signature validation, and content hashing—is the most effective defense against evolving PDF forgeries.